The digital landscape for mobile users has become increasingly precarious as commercial spyware entities adopt more aggressive and deceptive tactics to infiltrate devices.
Security researchers have recently identified another spyware manufacturer involved in a sophisticated campaign that uses fake Android applications to snoop on targets. This development underscores the persistent vulnerability of mobile ecosystems when users are lured away from official app stores through social engineering and deceptive marketing.
The latest campaign involves malicious apps that masquerade as legitimate services, including popular messaging platforms and customer support tools provided by telecommunications companies. By mimicking the visual identity of trusted brands, the spyware maker convinces users to sideload application packages that bypass the standard security checks of the Google Play Store.
Once installed, these applications grant the attacker near-total control over the infected device. Detailed reporting on this discovery can be found at TechCrunch.
Technical analysis of the spyware reveals a wide range of invasive capabilities designed for comprehensive surveillance. These include the ability to intercept and exfiltrate text messages, call logs, and contacts, as well as the capacity to capture real-time audio through the device microphone.
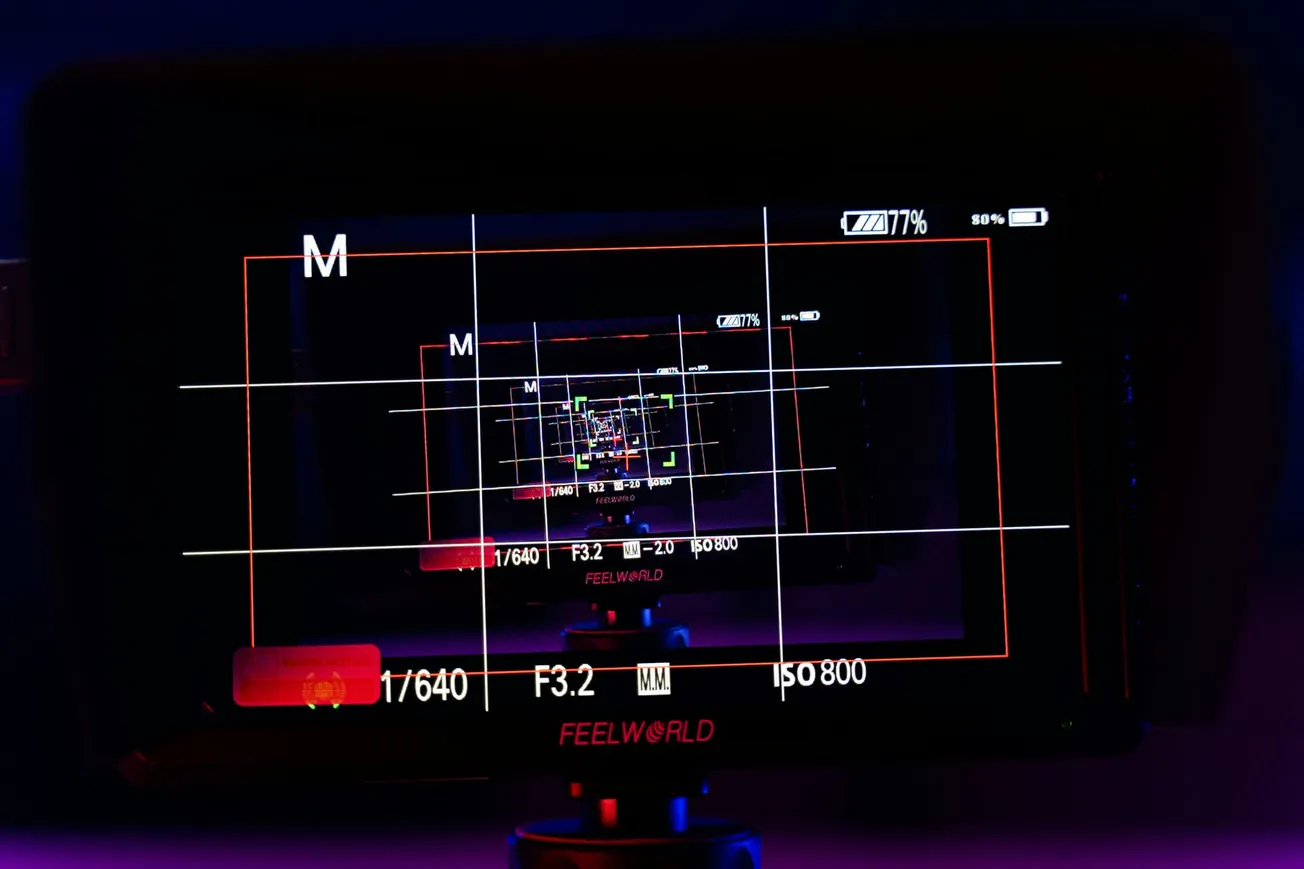
Furthermore, the malware can access imagery from both the front and rear-facing cameras, essentially turning the smartphone into a remote monitoring station. For business professionals and content creators who handle sensitive data or intellectual property, the presence of such tools represents a significant threat to operational security and personal privacy.
One of the most alarming aspects of this discovery is the use of snooping apps that claim to provide security or performance enhancements while doing the exact opposite. Some versions of the malware have been found posing as antivirus solutions or system updates, exploiting the user desire to protect their device.
According to industry analysis from the Electronic Frontier Foundation, this pedestrian hacking technique remains highly effective because it relies on human trust rather than complex software exploits.
To mitigate these risks, security experts recommend several critical practices for mobile hygiene:
- Avoid Sideloading: Only download applications from official sources like the Google Play Store, which employs advanced scanning to detect known malware signatures.
- Audit App Permissions: Be wary of apps that request access to the microphone, camera, or contacts when such permissions are not necessary for the app primary function.
- Monitor Device Behavior: Unusual battery drain, overheating, or unexpected data usage can be indicators of background spyware activity.
- Keep Software Updated: Ensure that the Android operating system and all installed apps are updated to the latest versions to benefit from the most recent security patches.
The proliferation of commercial spyware highlights a growing industry where software designed for law enforcement or government use frequently leaks into broader, more malicious applications. As noted in security bulletins from Kaspersky at securelist.com, the scale of these campaigns is massive, with hundreds of distinct malware builds surfacing in short periods.
This environment necessitates a proactive approach to security, especially for businesses that rely on mobile devices for internal communication and brand storytelling.
For organizations looking to secure their production workflows, understanding the threat landscape is the first step toward building a resilient digital infrastructure. By prioritizing official tools and maintaining strict security protocols, teams can protect their creative assets and ensure that their communication remains private.
To stay updated on the latest in mobile security and professional production tools, readers can explore the Business and Marketing sections at PodcastVideos.com. Protecting your device is essential to telling better stories and reaching wider audiences without the interference of malicious third-party actors.